...
Given the ease of availability of the Untangle NG Firewall, I used their SSL Inspector as an example. By default the Untangle SSL Inspector did not inspect traffic to https://badssl.com. As a result, I modified the default configuration of the SSL Inspector to inspect all HTTPS traffic. The other product tested is the Entensys UserGate UTM product, which also provides SSL inspection capabilities. Note that by default UserGate does not select the "Block sites with invalid certificates" option, meaning that the client is allowed to connect to sites with invalid certificates.
The client platform used for the test was Windows 7 with both Firefox 54.0.1 and Chrome 60.
...
Firefox 54.0.1 (Windows) | Chrome 60 (Windows) | UserGate Web Filter | UserGate Web Filter | ||||
|---|---|---|---|---|---|---|---|
| Certificate | |||||||
| expired | SEC_ERROR_EXPIRED_CERTIFICATE | NET::ERR_CERT_DATE_INVALID | Reset | Allowed | "Incorrect SSL certificate" | ||
| wrong.host | SSL_ERROR_BAD_CERT_DOMAIN | NET::ERR_CERT_COMMON_NAME_INVALID | Blocked | BlockedCertificate validation left up to client | |||
| self-signed | SEC_ERROR_UNKNOWN_ISSUER | NET::ERR_CERT_AUTHORITY_INVALID | Reset | Allowed | "Incorrect SSL certificate" | ||
| untrusted-root | SEC_ERROR_UNKNOWN_ISSUER | NET::ERR_CERT_AUTHORITY_INVALID | Reset | Allowed | "Incorrect SSL certificate" | ||
| revoked | SEC_ERROR_REVOKED_CERTIFICATE | NET::ERR_CERT_REVOKED | Allowed | Allowed | Allowed | ||
| pinning-test | MOZILLA_PKIX_ERROR_KEY_PINNING_FAILURE | NET::ERR_SSL_PINNED_KEY_NOT_IN_CERT_CHAIN | Allowed | Allowed | Allowed | ||
| no-common-name | Allowed | Allowed | Allowed | Allowed | Allowed | ||
| no-subject | Allowed | Allowed | Reset | Reset | Reset | ||
| incomplete-chain | Allowed | Allowed | Reset | Allowed | "Incorrect SSL certificate" | ||
| sha1-intermediate | SEC_ERROR_CERT_SIGNATURE_ALGORITHM_DISABLED | Allowed | Allowed | Allowed | Allowed | ||
| sha256 | Allowed | Allowed | Allowed | Allowed | Allowed | ||
| sha384 | Allowed | Allowed | Allowed | Allowed | Allowed | ||
| sha512 | Allowed | Allowed | Allowed | Allowed | Allowed | ||
| Allowed | Allowed | Allowed | Allowed | Allowed | |||
| 10000-sans | SSL_ERROR_RX_MALFORMED_HANDSHAKE | ERR_SSL_PROTOCOL_ERROR | Certificate validation left up to client | Blocked | Blocked | Blocked | |
| Allowed | Allowedecc256 | Allowed | Allowed | Allowed | |||
| ecc384 | Allowed | Allowed | Allowed | Allowed | Allowed | ||
| rsa2048 | Allowed | Allowed | Allowed | Allowed | Allowed | ||
| rsa8192 | Allowed | Allowed | Allowed | Allowed | Allowed | ||
| Cipher Suite | |||||||
| cbc | Allowed | Allowed | Allowed | Allowed | Allowed | ||
| rc4-md5 | SSL_ERROR_NO_CYPHER_OVERLAP | ERR_SSL_VERSION_OR_CIPHER_MISMATCH | Reset | Blocked | Blocked | ||
| rc4 | SSL_ERROR_NO_CYPHER_OVERLAP | ERR_SSL_VERSION_OR_CIPHER_MISMATCH | Reset | Blocked | Blocked | ||
| 3des | Allowed | Allowed | Allowed | Allowed | Allowed | ||
| null | SSL_ERROR_NO_CYPHER_OVERLAP | ERR_SSL_VERSION_OR_CIPHER_MISMATCH | Reset | Blocked | Blocked | ||
| mozilla-old | Allowed | Allowed | Allowed | Allowed | |||
| mozilla-intermediate | Allowed | Allowed | Allowed | Allowed | |||
| mozilla-modern | Allowed | Allowed | Allowed | Allowed | |||
| Key exchange | |||||||
| dh480 | SSL_ERROR_WEAK_SERVER_EPHEMERAL_DH_KEY | ERR_SSL_VERSION_OR_CIPHER_MISMATCH | Reset | Allowed | Allowed | ||
| dh512 | SSL_ERROR_WEAK_SERVER_EPHEMERAL_DH_KEY | ERR_SSL_VERSION_OR_CIPHER_MISMATCH | Reset | Allowed | Allowed | ||
| dh1024 | Allowed | ERR_SSL_VERSION_OR_CIPHER_MISMATCH | Allowed | Allowed | Allowed | ||
| dh2048 | Allowed | ERR_SSL_VERSION_OR_CIPHER_MISMATCH | Allowed | Allowed | Allowed | ||
| dh-small-subgroup | Allowed | ERR_SSL_VERSION_OR_CIPHER_MISMATCH | Allowed | Allowed | Allowed | ||
| dh-composite | Allowed | ERR_SSL_VERSION_OR_CIPHER_MISMATCH | Reset | Allowed | Allowed | ||
| static-rsa | Allowed | Allowed | Allowed | Allowed | Allowed | ||
| Certificate Transparency | |||||||
| invalid-expected-sct | Allowed | NET::ERR_CERTIFICATE_TRANSPARENCY_REQUIRED | Allowed | Allowed | Allowed | ||
| Defunct | |||||||
| sha1-2016 | SEC_ERROR_EXPIRED_CERTIFICATE | NET::ERR_CERT_WEAK_SIGNATURE_ALGORITHM | Reset | Allowed | "Incorrect SSL certificate" | ||
| sha1-2017 | SEC_ERROR_EXPIRED_CERTIFICATE | NET::ERR_CERT_WEAK_SIGNATURE_ALGORITHM | Reset | Allowed | "Incorrect SSL certificate" |
About the red "Allowed" items above
...
Here, the browser recommends that the user verify their internet connection and firewall, and run Windows Network Diagnostics. None of which will actually address the problem.
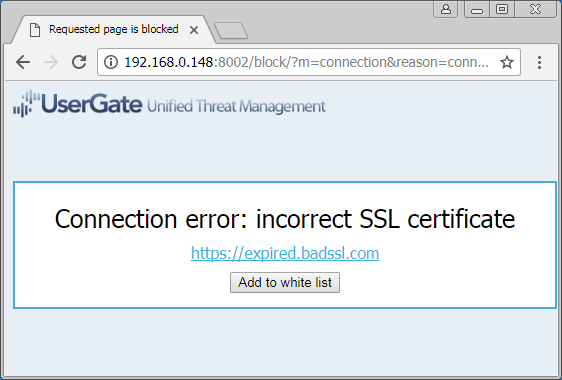
About the yellow "Incorrect SSL certificate" items above
When connecting via an Entensys UserGate proxy that has been explicitly configured to validate SSL certificates (the default is to allow invalid certificates), the user is presented with HTML content that indicates that the SSL certificate is "incorrect," without mentioning what the problem is. For example, Google Chrome connected via UserGate configured in such a manner:
Conclusion
As first mentioned in the 2015 blog post The Risks of SSL Inspection, the ability to inspect HTTPS traffic does not come without its costs. Given the ease of testing the impact with the badssl.com website, this impact is now easier for users and network administrators to determine. The table above currently only contains results for the Untangle SSL Inspector product, however other similar products have similar results. HTTPS inspection is not something that can be done at the network level without negatively affecting the security of the clients.
...